If this was an article about the NBA or the NFL, we'd be writing something like this: "SamSam has just signed a two-year deal worth $5.9 million...."
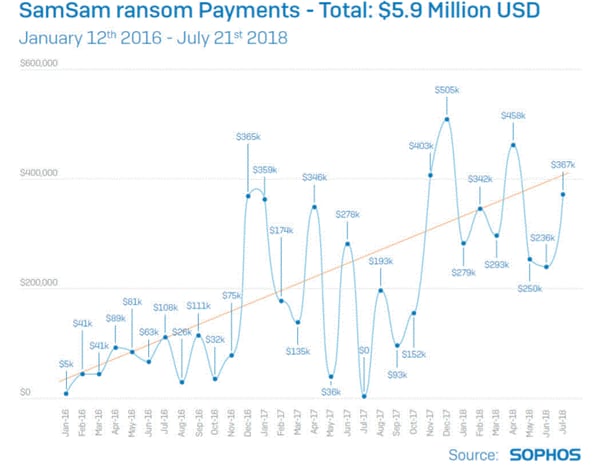
That is because, according to security researchers, SamSam ransomware attacks have netted the hackers behind it at least $5.9 million in ransom payments during the last two and a half years.
Those payments were in Bitcoin, of course, so researchers had to do some math. But you get the point. Sadly, in this case, crime does pay.
10 things about SamSam ransomware
Here are 10 new facts about SamSam ransomware according to researchers at Sophos, which just issued an extensive research report.
1. 74% of the known victims are based in the United States.
2. Total KNOWN ransoms paid are $5.9 million equivalent in Bitcoin. The profits break down like this:
 3. Other regions known to have suffered attacks include Canada, the UK, and the Middle East.
3. Other regions known to have suffered attacks include Canada, the UK, and the Middle East.
4. The largest ransom paid by an individual victim, so far, is valued at $64,000 US, a larger number than most ransomware families can demand.
5. Medium to large public sector organizations in healthcare, education, and government make up 50% of identified victims; the rest are in a long list of verticals in the private sector.
6. The attackers carefully choose their targets and spread quietly through legitimate network admin tools to avoid detection.
7. Attackers also focus on timing, typically launching encryption commands in the middle of the night or the early hours of the morning of the victim’s local time zone, when most users and admins would be asleep.
8. Unlike most other ransomware, SamSam encrypts more than document files, images, and other personal or work data. It also encrypts configuration and data files required to run applications (e.g., Microsoft Office). This means victims whose backup strategy only protects the user’s documents and files won’t be able to recover a machine without reimaging it first.
9. Every subsequent attack shows a progression in sophistication, and it appears the operators of SamSam ransomware understand operational security.
10. SamSam pricing is trending upward. Attackers are charging more ransom then they used to.
SamSam ransomware 3.0 file names
Sophos researchers, who've been hot on the trail of SamSam's operators for more than two years now, also came across a few intriguing things on file names and extensions being used by the ransomware.
First of all, it appears the SamSam operators are watching Sophos research.
In the July 2018 version of SamSam, which you might call SamSam 3.0, one of the files has a .sophos extension. This seems to be a tip of the hat to the researchers, does it not?
And researchers also say new file names include things like SORRY-FOR-FILEs.html and .weapologize that may sound cute but change nothing about the damage and costs this ransomware strain has done to so many organizations.
In 2018 alone, we know of a slew of SamSam victims who have gone public: Allscripts, Adams Memorial Hospital, the City of Atlanta, the Colorado Department of Transportation, and Mississippi State Valley University.
And researchers note that about 50% of SamSam victims have never revealed the fact they are a victim.
For many more details on favorite SamSam attack methods, what code looks like, and other research, check out the new Sophos study on SamSam.



