Do you need quotes about cybersecurity for a presentation? Are you looking for InfoSec quotes to inspire you and your cybersecurity team, or to paint a picture for the board?
Well, we have a baker's dozen of them.
Here are 13 great cybersecurity quotes overheard at SecureWorld's regional cybersecurity conferences across North America during the past few months.
#1 Deneen DeFiore, SVP and Chief Information & Product Security Officer at GE Aviation, on cyber as a business requirement:
"Every two seconds, a commercial aircraft powered by GE takes off. We invent the future of flight, we lift people up, and we bring them home safely. What I tell my team is we secure that purpose and mission. Cyber is now a criteria of the way we do business, and who we choose to do business with along all of our operations."
#2 Jimmy Sanders, VP of Information Security at Netflix DVD, on making sure InfoSec is about business enablement:
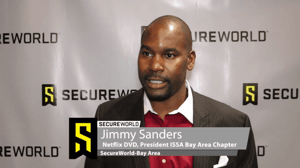 "My job is to ensure that our security maintains the culture and the vision of our origins. Our culture is based on two aspects, it’s called freedom and responsibility. We will give developers, engineers, we’ll give different practitioners the freedom to do what they want to do. But it’s their responsibility to do it to a certain standard. And so my security tools have to be in lockstep with that. My tools can’t block them from the freedom that is a core tenant of Netflix."
"My job is to ensure that our security maintains the culture and the vision of our origins. Our culture is based on two aspects, it’s called freedom and responsibility. We will give developers, engineers, we’ll give different practitioners the freedom to do what they want to do. But it’s their responsibility to do it to a certain standard. And so my security tools have to be in lockstep with that. My tools can’t block them from the freedom that is a core tenant of Netflix."
#3 Mike Muha, CISO and Chief Privacy Officer (CPO) at WorkForce Software, on how security leaders increase the odds of getting budget approval:
"You want to build that trust with other people in the company, too. Because if they trust you, you do the right thing, you do things on time, you have good ideas, then its more likely that when you ask for security spend it’s a valid spend that should be taken seriously. So, that’s really important, building relationships and that’s hard to do for a lot of people who are engineers at heart."
#4 Brian Gorenc, who runs the Zero Day Initiative, which is the world’s largest vendor-agnostic bug bounty program and operates inside Trend Micro. He explains how bug bounty programs are disrupting cybercrime:
"The impact is significant, if you think about it, every patch that is coming out, especially when it comes to enterprise software and operating systems, it is being fed by bug bounty programs. The community is coming together to make sure the vendors are actually releasing patches for these bugs and as a result the attack surface shifts and changes. We see that in the way people are using exploits in the wild because they have to go after different things because the old vulnerabilities are no longer there."
#5 Justin Berman, CISO at Zenefits, on the importance of constant testing of security controls:
"I think continuous testing is really important because adversaries behaviors change frequently, our profiles and organizations change frequently and more importantly, even than the changes they bring and the changes in the playbooks we face is ultimately the controls and their effectiveness are easy to lose track of. And so when I think about testing constantly, it is because I want to know more up to the minute than up to the month how our controls are performing."
#6 Shawn Tuma, cybersecurity and data privacy attorney at Spencer Fane LLP, on security's frequent lack of strategy:.png?width=300&name=SPEAKER-GRAPHIC-TEMPLATE-Shawn-Tuma%20(2).png)
"We always talk about there’s a lack of funding, a lack of support, a lack of tools and gadgets or gizmos, but when I look back at the 19 years I’ve been doing this and see where are the real weaknesses, it’s usually a lack of strategy. It’s that we have all this stuff in place, but we don’t have a head coach who’s seeing the whole playing field, who understands where all the pieces fit together and who has devised a strategy to make it all work."
#7 Rebecca Herold, CEO of The Privacy Professor, on why the growth of IoT devices is a threat to security and safety:
“For most smart devices being made, there’s likely someone in the world reverse engineering it to see how to get in. This includes implanted medical devices, where privacy and security concerns are significant."
#8 Tamika Bass, CISO at the Georgia Department of Public Health, on the privacy and security challenges in healthcare:.jpg?width=170&name=0218a961-d50e-4881-997a-5e2b5668a572-headshot-TamikaFinal-(1).jpg)
"You can fix things that happen with your Social Security Number, you can get a new credit card when your card information is compromised. But when your protected health information is compromised, it’s a totally different situation."
#9 Zoe Lindsey, Customer Advocacy at Duo Security, on Zero Trust:
"Zero Trust is not a product. It is a philosophy and a model."
[RELATED: Web conference on-demand: Practical Steps to Zero Trust]
#10 Bruce Lobree, Cybersecurity Architect at Symetra Life Insurance Company, on who is the weakest link in cybersecurity:
"What are we doing wrong? Not what are users doing wrong. It is really important that security professionals put that mirror up."
#11 Matthew Gardiner, Director of Product Marketing at Mimecast, on the size of the phishing problem:
"Approximately 46,000 new phishing sites are created every day, and on average, they are only active 4-8 hours."
#12 Col. Cedric Leighton (Ret.), CNN military analyst and cyberwarfare expert, on how corporations will have to think differently to fight back against cybercrime:
"Corporations have increasingly important roles in cyber conflicts. As they increase in power relative to nation-states, corporations are increasingly where both the money and the power reside. Most companies don’t want to think like intelligence agencies, but since the new “currency of the realm” is data, they are going to have to think and act like the intelligence agencies of nation-states."
#13 Brent Lassi, CISO at Bluecore, on a CISO Stop List he believes every leader in security should have:
"The way I’ve taken to start that process and not become obsolete is to say what have we been doing that we don’t need to do anymore. What are we doing that’s bad behavior? Being a curmudgeon, selling fear, not bringing solutions, not listening to our vendors, hiring too many engineers and not enough programmers in security. Some people say, what?! Because we’ve traditionally been engineers not developers, but to play in that new space you need to start re-tooling so my stop list is 20 things across culture, strategy, philosophy and technology, that organizations can stop doing. But it’s just a start, these are the 20 I’ve come up with. What I want is everybody to go back to their own organization and come up with their own stop list. Make their own whiteboard list of all the things they do and ask, do we need to do that? Do we need to do that, differently?"
Looking to share best practices and viewpoints like these?
Then consider yourself invited to join your peers at the 2019 SecureWorld conference in your region.
[RELATED: 20 cybersecurity quotes everyone in security should read]




