Gregg Braunton believes in the power of "visual" Incident Response.
"Storyboarding during incident response is natural, and will make your response much more effective," he says.
Braunton is the National Director of Threat Management, Incident Response & Forensics at Catholic Health Initiatives, one of the largest health networks in the United States.
During the SecureWorld web conference on cyber Incident Response (IR), he drove home the value of the storyboarding approach to IR.
Incident Response: Is your plan visual?
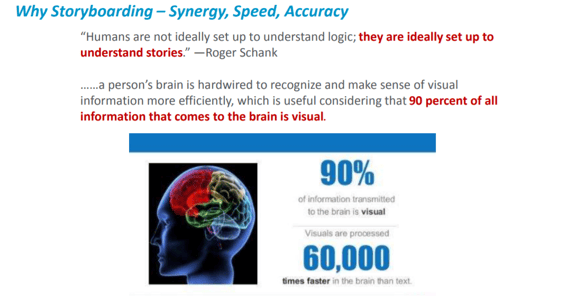
Braunton says storyboarding plays to our human wiring, in which visuals are processed 60,000 times faster than text. And he says a visual approach increases synergy, speed, and accuracy during a response.
He gave an example of the typical "linear" way of IR with a few lines of text on the incident:
And he compared that to "storyboarding IR" his team uses to diagram the incident response: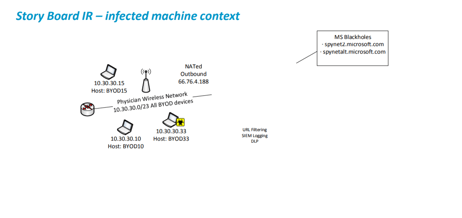 He says his team uses Visio for storyboarding, WebEx for real-time collaboration, and OneNote to share and update documents across the team.
He says his team uses Visio for storyboarding, WebEx for real-time collaboration, and OneNote to share and update documents across the team.
And all of this is key for potential litigation or communications following a cyber incident. "You need to make sure you're documenting the components that will allow you to
Incident Response: Does your plan include legal and communications?
Attorney Katherine Britton emphasized the importance of having an IR plan so you're not trying to create one during an incident.
And during an incident, she says get Legal involved right away to analyze the significance of what has happened from a reporting standpoint:
"What exactly was taken, and then what form was it in? Was it encrypted? If not, it’s more likely a reportable breach."
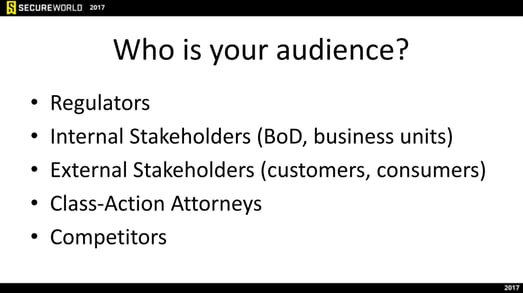
Also in your IR plan, there must be a communications framework. That way you know who will communicate to your various stakeholders and what should be said.
Incident Response: Does your plan integrate IR and security operations?
Organizations often divide Incident Response and Security Operations into two separate teams. While this allows for focused expertise, it can create a disjointed, ineffective process.
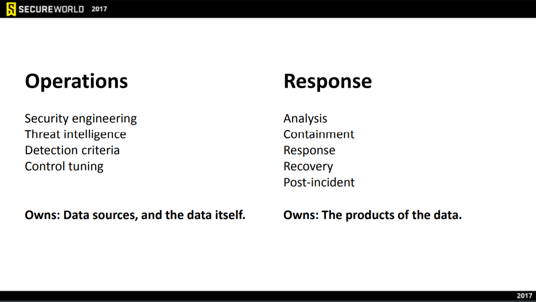
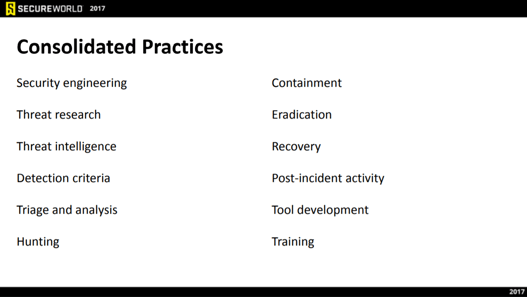
"The vast majority of companies we work with do not have the budget or the people to build both of these teams."
So he suggested ways a security team can consolidate practices and what that breakdown might be like.
These are just a few nuggets that came out of the SecureWorld web conference. There's a lot more gold to mine by listening on-demand right now.