When it comes to real-time cyber attack maps, some are funny, some seem ominous, and all of them tell a story that words alone cannot: cyber attacks never stop.
7 live cyber attack threat maps in 2020
1. Our favorite real-time worldwide
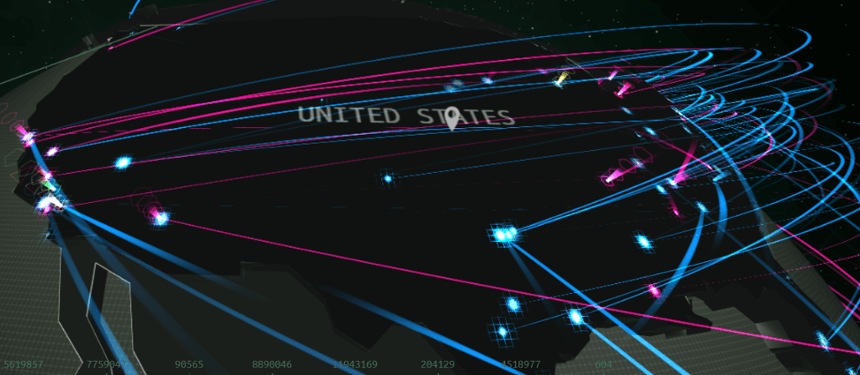 Kaspersky Lab cyber attack map: https://cybermap.kaspersky.com/
Kaspersky Lab cyber attack map: https://cybermap.kaspersky.com/
2. Next, how about a live botnet threat map? Put on some classical music to go with this one and you'll have your own synchronized "attack show" of real-time botnet attacks around the globe.
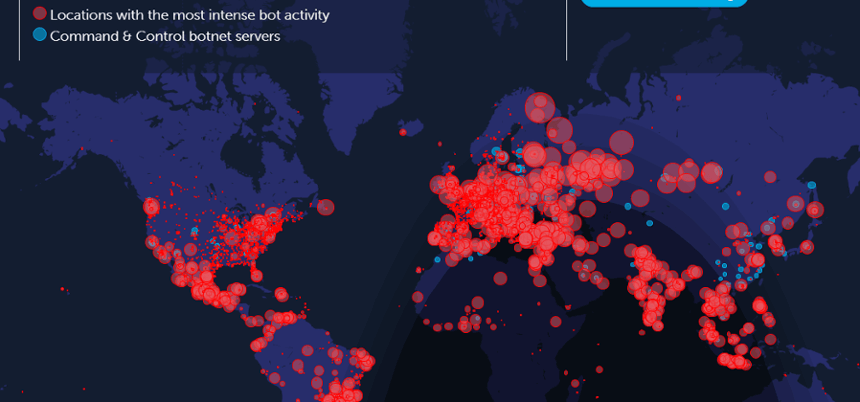 Deteque botnet threat map: https://www.deteque.com/live-threat-map/
Deteque botnet threat map: https://www.deteque.com/live-threat-map/
3. Next is the Fortinet real-time attack map. It may not be the most exciting visually, but there are a couple of cool features that make it unique. The bottom left-hand corner has easy to understand (and dramatic) cyber attack statistics, and if you look at the map you'll see a day/night map is subtly overlayed onto the cyber attack map. So you can see where bad actors like to work after dark.
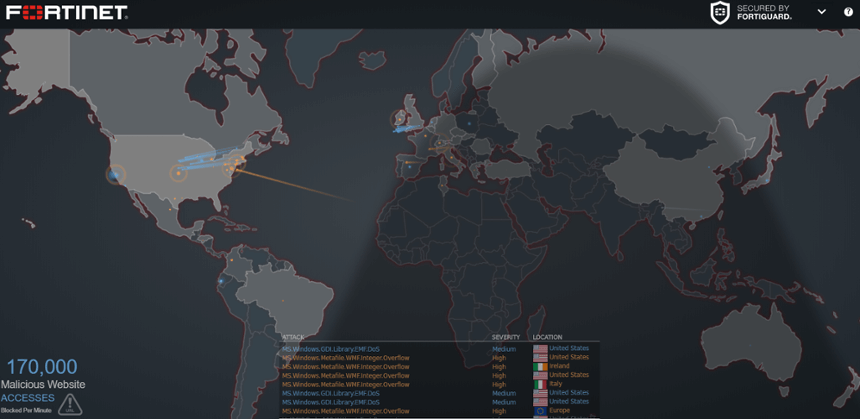 Fortinet live cyber attack map: https://threatmap.fortiguard.com/
Fortinet live cyber attack map: https://threatmap.fortiguard.com/
4. There's a little more color in our next map from FireEye. Here's what sets this one apart: It is less dramatic with its attack graphics than some of the others, and it also shows the top attacked verticals for the past 30 days.
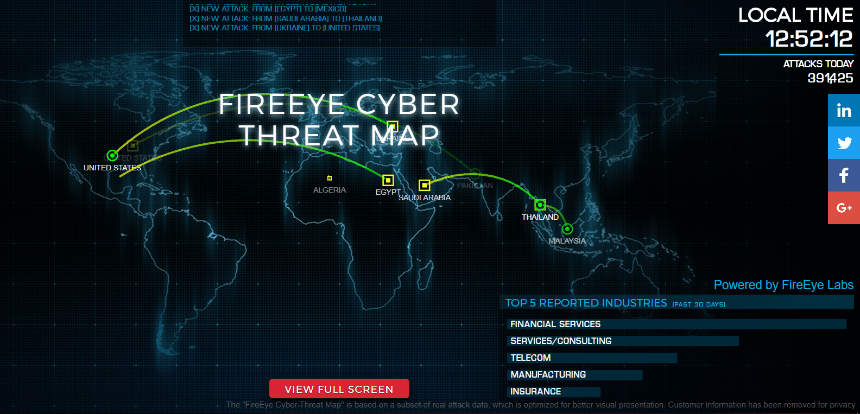 FireEye real-time cyber attack map: https://www.fireeye.com/cyber-map/threat-map.html
FireEye real-time cyber attack map: https://www.fireeye.com/cyber-map/threat-map.html
5. We also discovered Bitdefender's real-time cyber threat map, which claims to show infections and attacks. Plus, its rapid-fire list of attacks drives home the point for non-technical folks.
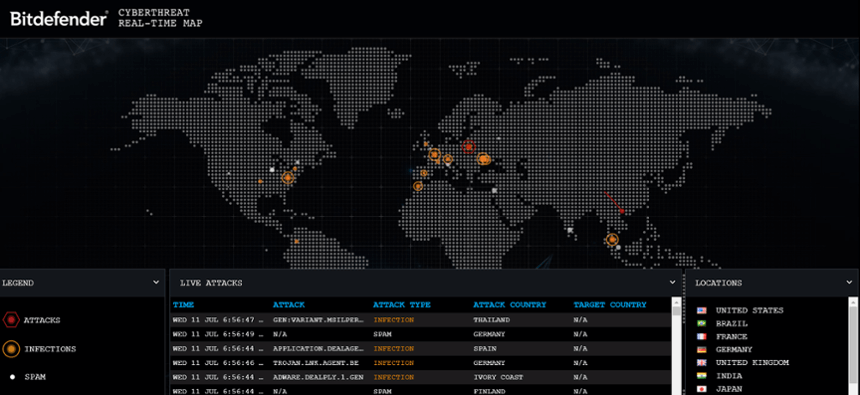 Bitdefender live cyber threat map: https://threatmap.bitdefender.com/
Bitdefender live cyber threat map: https://threatmap.bitdefender.com/
6. Another really good looking live cyber attack map is from SonicWall, which was pointed out by a SecureWorld reader. We really like the easy to scan analytics at the bottom of the map which shows which countries are top attack targets right now and the average number of cyber attacks per site for the day, among other things.
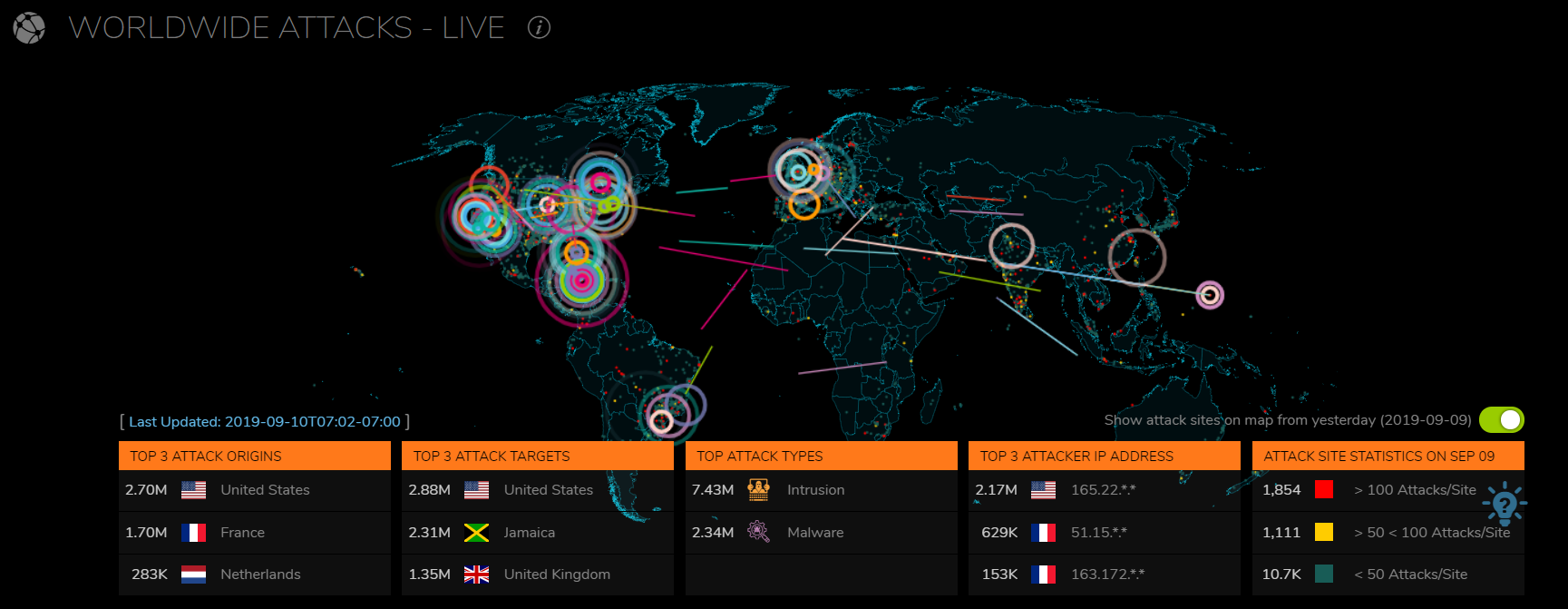
SonicWall live cyber attacks map:
https://securitycenter.sonicwall.com/m/page/worldwide-attacks
7. The last one is what you might call an InfoSec classic. Not only does this cyber threat map include the "pew-pew" sound of video games from the '80s, but it flat out says its data comes from the cloud, including the cumulus cloud! And it translates the attacks it is supposedly tracking into phrases like "it's cyber Pompeii" or "we'll just call it a glitch."
 With a name like
With a name like
https://threatbutt.com/map/
Did we miss a cyber threat map that you like? Let us know in the comments below. Or tell us in person at one of our 17 regional SecureWorld cybersecurity conferences!
New podcasts: Nation-State cyberattacks
Super power face-offs used to be about who had the most military might. Increasingly, however, the battle front between nations has shifted to what military leaders call the 5th domain: cyberspace.
Listen to our podcast with CNN Military Analyst and cyber expert Colonel (USAF, Ret.) Cedric Leighton.
He explains what China, Iran, North Korea and Russia are going after when they launch cyberattacks against the United States and the western world.
Also, it was likely nation-state hackers that launched a cyberattack against the World Health Organization during the coronavirus pandemic. We talked to the man who discovered the attack:




