A privilege escalation flaw on Google Android OS was disclosed this week without a patch from Google, leaving some in security circles to ask why.
The vulnerability allows attackers who have some sort of untrusted code with low privileges on an Android device to gain access to privileged parts of the Android kernel.
The Zero Day Initiative disclosed the vulnerability:
"The specific flaw exists within the v4l2 driver. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this to escalate privileges in the context of the kernel."
Android vulnerability disclosed without a patch: why?
So why was the Android vulnerability disclosed without a patch?
After all, the Zero Day Initiative (ZDI) was created to encourage the "reporting of 0-day vulnerabilities privately" to the affected vendors by financially rewarding researchers.
Well, that's what the ZDI did; it privately notified Google.
In fact, the Zero Day Initiative detailed months of communication with Google ("the vendor"):
- 03/13/19 - ZDI reported a vulnerability to the vendor
- 03/13/19 - The vendor acknowledged and requested further information
- 03/25/19 - ZDI provided the requested details
- 06/28/19 - The vendor confirmed the vulnerability would be fixed, but did not provide an estimated time frame
- 07/12/19 - ZDI requested an estimated date for the fix
- 07/12/19 - The vendor indicated they could not specify a date
- 08/21/19 - ZDI requested an update
- 08/26/19 - The vendor indicated there were no further updates
- 08/28/19 - ZDI notified the vendor of the intention to disclose the report as a 0-day advisory
It appears, to the casual observer, that Google decided not to issue a patch, or at very least will not indicate if it plans to do so.
How can you mitigate this Android OS vulnerability?
The ZDI says right now, there appears to be a single option:
"Given the nature of the vulnerability, the only salient mitigation strategy is to restrict interaction with the service. Only the clients and servers that have a legitimate procedural relationship with the service should be permitted to communicate with it."
The Zero Day Initiative is the world’s largest vendor-agnostic bug bounty program.
[RELATED: Bug Bounty Programs Are Working: Here's Proof]
Bruce Schneier on patching: nearing the end
Situations like this shine a spotlight on patching as a tool for organizations and security teams.
We interviewed cybersecurity thought leader Bruce Schneier at SecureWorld Boston about strong comments he's made regarding patching.
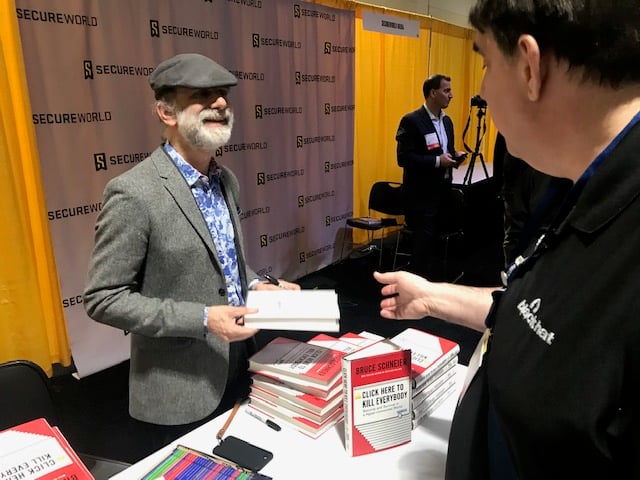
We read in one of his books that he calls patching, "A failed security paradigm," so we asked him about it:
"You know, patching is kind of reaching the end of its useful life. It works, really, because the things we're patching are expensive and maintained by tech companies. They're laptops, they are computers, they are phones. And that whole patching ecosystem is predicated on there being engineers at Apple and Microsoft and Google who can write these patches and push them down," says Schneier.
"You start moving to low-cost embedded systems like DVRs and home routers and appliances, and there are no engineers to write patches. There's no mechanism to get the patches to the systems. So that, that's going to fail pretty badly."
And in a case like this, the vulnerability remains altogether unpatched—at least for now.




