One year ago, the Pentagon asked white hat hackers to bring their best and try to hack the U.S. Department of Defense and branches of the military.
Now the results of that effort are in: they uncovered thousands of true vulnerabilities and collectively cashed out more than $300,000 through a bug bounty program known as "Hack the Pentagon" run by bug bounty platform HackerOne.
" The first report was submitted 13 minutes after launch, and within 6 hours, that number grew to nearly 200," says the company.
"Of these vulnerabilities, over 100 have been high or critical severity issues, including remote code executions, SQL injections, and ways to bypass authentication."
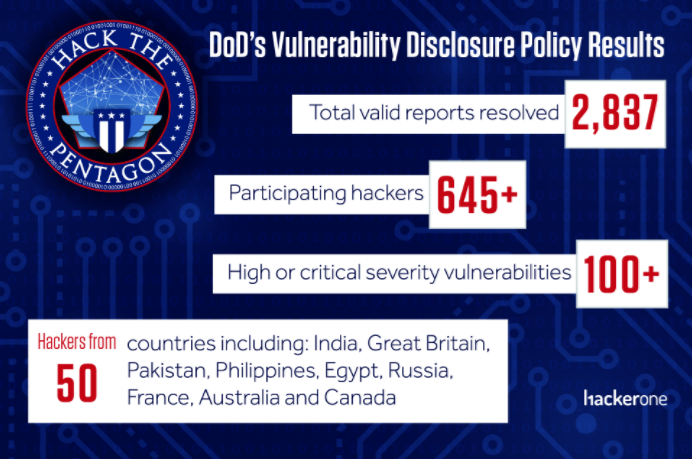
Although the company says the largest number of hackers involved are based in the United States, white hats from around the world were part of the program.
What difference
“By allowing outside researchers to find holes and vulnerabilities on several sites and subdomains, we freed up our own cyber specialists to spend more time fixing them than finding them,” says former Secretary of Defense, Ash Carter. “The (program) showed us one way to streamline what we do to defend our networks and correct vulnerabilities more quickly.”
As you can imagine, this program has been extended and expanded to include Hack the Army, Hack the AirForce and other government agencies.
In total, HackerOne has paid out $20 million in bug bounties since its founding in 2014.




