Business Email Compromise is becoming more sophisticated.
Hackers leverage information on social media, public announcements by organizations and even compliance requirements, all in an effort to social engineer victims.
Rebecca Rakoski, Managing Partner XPAN Law Group, says BEC is both a technological and emotional challenge for organizations.
"Companies who are rightly focused on security should be saying something like this: I've got great security. But I've also got Dave, the happy clicker who is clicking on things and not thinking about cybersecurity."
She talked about this during NextGen Business Email Compromise, a SecureWorld web conference now available on demand.
And Rakoski also shared 5 top ways her cybersecurity firm sees social engineering in use and she unpacked each of these terms:
"Pretexting can be providing an attack pretext, making an employee feel secure as to whom the person is on the other side, by impersonating a person of authority, a friend or someone they trust. A message from an investigator who will be performing a compliance audit, for example."
Cybersecurity attorney Shawn Tuma, with SpecerFane, spent much of his session updating developments in litigation in the area of security awareness and BEC. And he also looked at the consequences of being social engineered using a couple of popular attacks that are being used. This includes the requests for fake payment instructions as a phishing tactic.
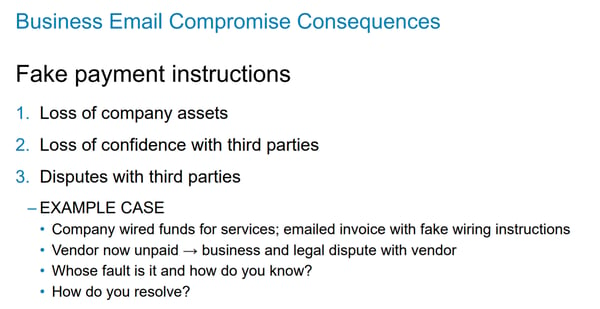
"The odds are really, really good you'll never get that money back. And even if you have cybersecurity insurance, you may not have social engineering coverage. Especially because many policies see this as a voluntary act since your employee initiated the transfer. And what follows is you still owe money to the legitimate party and there is no clear, easy way to resolve it. This is where litigation comes from."
Defending your organization against business email compromise
Know Be 4 Security Awareness Advocate Erich Kron says a challenge for organizations now is that many underestimate the sophistication and urgency of these attacks.
"Sophisticated hackers have moved way beyond misspelled poorly formatted emails. Now, they turn the tables on employees, often by using fear as a trigger as if that person needs to act right now to avoid consequences for the organization or the employee."
He also shared excellent examples of the threat landscape in this area of attacks.
So how do you defend your organization against BEC attacks? Kron listed a number of ways, including 2FA, and then he covered his number one approach: arming your employees for battle.
However, like a normal army, one weapon is not enough. Here is what he sees working:
We can't say enough about the quality of this business email compromise web conference. Check it out for yourself, on demand.
And join security leaders at a regional 2019 cybersecurity conference near you, to continue this conversation and increase your trusted network of peers.




