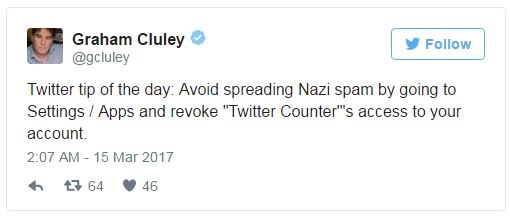
As British cyber guru Graham Cluley stepped off a plane into Kuwait City Wednesday morning, he turned on his phone and was greeted with a slew of messages notifying him that his Twitter account had been hacked.
Even worse, it had been defaced with Nazi propaganda.

He hadn't clicked on any suspicious links (especially not while his phone was on airplane mode), and according to his site, two-step verification was turned on.
So what happened?
A third-party app called Twitter Counter happened. It requests read and write permission in order to count your Twitter followers.
Cluley gave it access to his account in October 2014. While the app didn't have his Twitter password, it also didn't need to follow the two-step verification process to access his account.
Nathan Wenzler, Chief Security Strategist at AsTech, said, “I’m not surprised at all that this happened. Many hacks follow this type of attack sequence. It's easier to break into something less defended, which already has access to where you want to ultimately break in than it is to go after the well-protected application directly. Using a flaw in Twitter Counter to then gain access to accounts which live in Twitter absolutely follows an attack chain I would expect."
To prevent this type of attack from happening again, it's important for app developers to ensure their code is secure.
While users need to be careful about which permissions they allow access to their accounts, the responsibility for security lies on Twitter. The app needs to ensure the validity of third-party apps they are integrating with, and make sure that a compromised account doesn't turn into a full-blown takeover.




