Security researchers at Trend Micro just issued their 2019 Midyear Security Roundup report, and two types of cyberattacks are surging right now according to the company's research.
Fileless attack statistics 2019
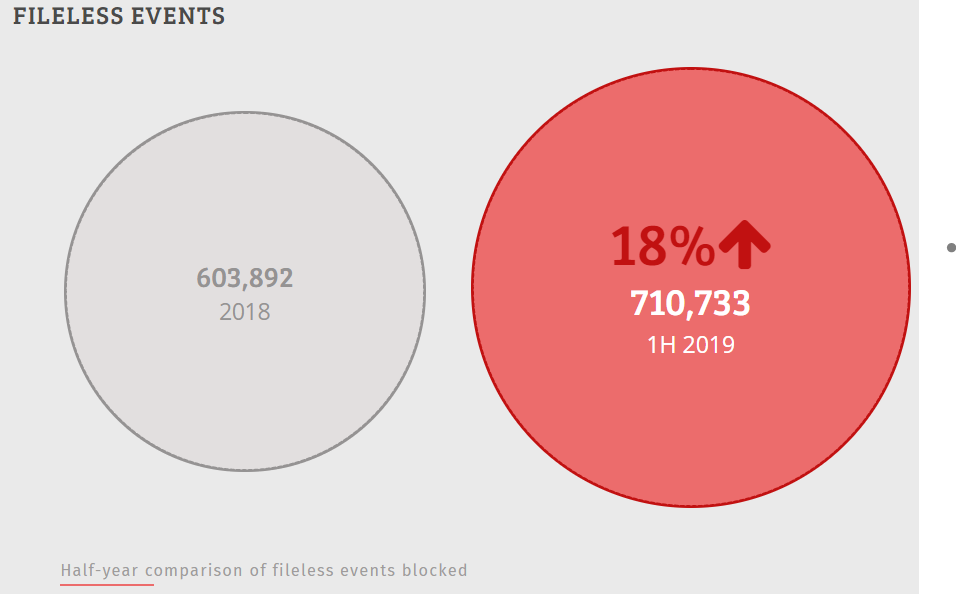
The report revealed that fileless attacks are sharply on the rise. This type of cyberattack shot upward 18% in the first half of 2019 compared to the last half of 2018.
These type of attacks live off the land, as in other processes or parts of a system:
"... so-called fileless threats are not as visible as traditional malware since these typically do not write to disk, are usually executed in a system’s memory, reside in the registry, or misuse normally whitelisted tools like PowerShell, PsExec, or Windows Management Instrumentation."
And there is another type of attack that is surging: ransomware.
Ransomware statistics 2019
The report also backs up what we've been publishing so much about in 2019: a spike in ransomware attacks, like the one that suddenly canceled school for thousands.
Trend Micro found a 77 percent surge in ransomware attacks during the first half of 2019, even though fewer new ransomware families are being detected:

Researchers say that WannaCry is still the most prevalent type of ransomware.
They also detailed harmful actions of other ransomware families which go beyond encrypting data. And they detailed how the attack likely arrives.
Here are three examples.
How Ryuk ransomware works
- Ryuk ransomware often arrives through spam
- Ryuk can render infected systems unbootable
How LockerGoGa ransomware works
- LockerGoGa ransomware arrives via compromised credentials
- Modifies the passwords of infected systems' user accounts, prevents infected systems from being rebooted
How RobbinHood ransomware works
- RobbinHood arrives via insecure remote desktops or trojans
- Encrypts each file with a unique key
The reason behind all these varying tactics is the same, according to researchers:
"Some ransomware variants... were designed with notable features that decreased the chances of victims recovering files and systems."
There is much more to this report entitled "Evasive Threats, Pervasive Effects."
[RELATED: Business Email Compromise Tops Cyber Insurance Payout Claims]




