As vaccines for COVID-19 are being distributed around the world, it appears the end of this global pandemic is on the horizon. But cybercriminals are still taking advantage of every moment they can.
The U.S. Attorney's Office for the District of Maryland seized two domain names, modernatx.com and regeneronmedicals.com, for spoofing and imitating websites of real biotechnology companies that have developed vaccines.
Investigators say the fake websites were created for the purpose of collecting personal information of those who visit the sites, and then using that information for fraud, phishing attacks, deployment of malware, and other malicious reasons.
COVID-19 cybercrime: fake biotech domain names seized
The investigations into the fake websites began in early December of this year. One of the sites was discovered after corporate security from one company notified Homeland Security Investigation's (HSI) Intellectual Property Rights Center (IPRC) and the Cyber Crimes Center (C3). The other website was discovered through an ongoing investigation by C3.
HSI Baltimore Special Agent in Charge John Eisert had this to say regarding the seizure of the fake websites:
"These individuals took advantage of fear during the global pandemic and attempted to steal personal information for nefarious purposes. From the cyber realm to counterfeit medication to financial crime, Homeland Security Investigations is committed to detecting, investigating, and disrupting all types of fraud related to the COVID-19 pandemic."
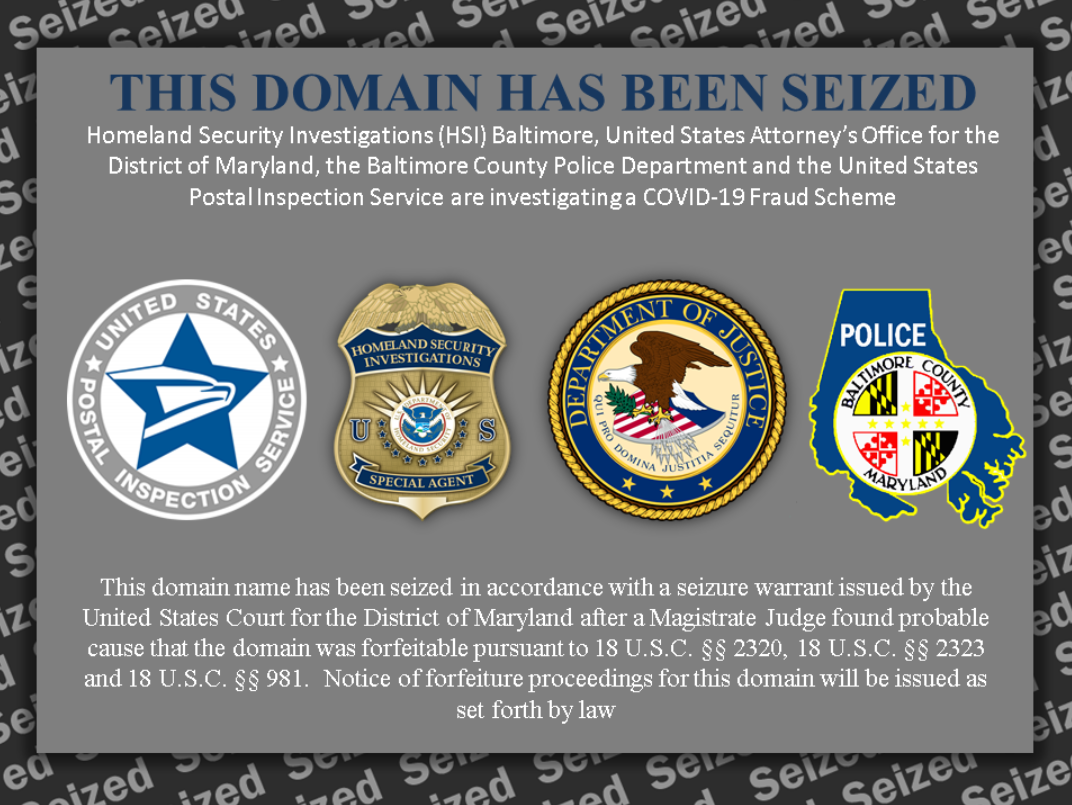
Here is a screenshot of what you now see if you to try to access one of these domains:
Coronavirus cyber fraud: how the websites were seized
On December 10, the Global Head of Corporate Security for Moderna notified the HSI IPRC and C3 that the company's cybersecurity team found the domain name modernatx.com to be fraudulently representing the company.
The fake website displayed the name and trademarked logos of Moderna, as well as logos, markings, colors, and text that showed no obvious differences between the real website and the fake one. The only major difference was a slight misspelling of the company's name.
Unlike the real domain, when users clicked on the "Contact Us" tab, they were redirected to a page that requested personal information, like name, email, phone number, and company.
Further investigations into the domain revealed that it was registered on December 8, through a company headquartered in Kuala Lumpur, Malaysia, with no personal information for the registrar listed.
The second domain name seized, regeneronmedicals.com, fraudulently represented the website for Regeneron. HSI C3 was conducting an investigation into malicious websites when they discovered this fake domain on December 9.
It represented the company in the same way as the first domain name seized, however the "Contact Us" tab directed "Healthcare professionals, patients or caregivers requesting specific product information, reporting an adverse event or reporting a product complaint" to contact the "Medical Department" at the Voice over IP (VoIP) number, which was not listed on the real domain.
Investigators found the fake domain was registered on December 6 by an individual in Onitsha Anambra, Nigeria.
Related podcast: COVID-19 related cybercrime
For more examples of how cybercriminals evolved right along with the coronavirus pandemic, listen to the following podcast, where we interview Myla Pilao of Trend Micro. Her Threat Research Team tracks more than five billion cyber threats each day.





