One of the coolest things about Etsy.com is that it allows bakers and craft makers from around the world to create their own online store within the platform.
The result is that you can find unique gifts and the creatives behind each store can reach a market they never could have without the eCommerce site.
Now, U.S. officials have revealed details of what sounds like Etsy's evil twin.
Etsy's evil twin, making money for hackers and criminals
The site is called DEER.IO and it allows cybercriminals to create a store on the platform to sell their hacking products and services. Some of it may even be your data.
"DEER.IO started operations as of at least October 2013, and claims to have over 24,000 active shops with sales exceeding $17 million to date."
The U.S. Department of Justice revealed more about the site this week when it charged Kirill Victorovich Firsov with running DEER.IO.
What could you buy on the hacking marketplace?
The new court documents reveal the type of information you can purchase from the website:
"DEER.IO virtual stores offer for sale a variety of hacked and/or compromised U.S. and international financial and corporate data, Personally Identifiable Information (PII), and compromised user accounts from many U.S. companies. Individuals can also buy computer files, financial information, PII, and usernames
and passwords taken from computers infected with malicious software (malware) located both in the U.S. and abroad."
The DOJ says FBI agents from San Diego went shopping on the site. The items they purchased reveals how affordable it is to buy stolen data and account information:
"On or about March 4, 2020, the FBI purchased approximately 1,100 gamer accounts from the DEER.IO store ACCOUNTS-MARKET.DEER.IS for under $20 in Bitcoin."
Investigators then confirmed that hundreds of these were legitimate accounts that had been hacked. And then the agents continued to shop:
"On or about March 5, 2020, the FBI purchased approximately 999 individual PII accounts from the DEER.IO store SHIKISHOP.DEER.IS for approximately $170 in Bitcoin. On that same date, the FBI purchased approximately 2,650 individual PII accounts from the DEER.IO store SHIKISHOP.DEER.IS for approximately $522 in Bitcoin. From those identities, the FBI identified names, dates of birth and U.S. Social security numbers for multiple individuals who reside
in San Diego County."
Agents apparently used the site's search feature, which allows you to search for hacked data by company name or geographic location.
You can also buy "hacker-for-hire" services on the platform.
What is the business model for the cybercrime website?
According to the U.S. DOJ, DEER.IO has a business model that makes its owner a lot of money in subscription fees. Who doesn't have subscription fees these days?
"A cybercriminal who wants to sell contraband or offer criminal services through DEER.IO can purchase a storefront directly from the DEER.IO website for 800 Rubles (approximately $12.50) per month. The monthly fee is payable by Bitcoin or a variety of online Russian payment methods such as WebMoney, a Russian based money transfer system similar to PayPal."
And once you make the payment, this site for hackers helps you get up and running in just a few clicks:
"Once shop access is purchased via the DEER.IO platform, the site then guides the newly-minted shop owner through an automated set-up to upload the products and services on offer through the shop and configure crypto-currency wallets to collect payments for the purchased products and/or services."
Who is the operator of the cybercrime eCommerce site?
The U.S. Department of Justice reveals very little about the man who runs the site.
"Kirill Victorovichv Firsov is a Russian cyber hacker, and the administrator of the DEER.IO cyber platform. Firsov not only managed the platform, he also advertised it on other cyber forums, which catered to hackers."
The DEER.IO platform is maintained on Russian servers and currently out of reach of the U.S. government.
Why charge hackers and cybercriminals if we cannot get them?
If the DEER.IO servers are out of reach, and the Russian man behind the criminal enterprise is also out of reach, why bother with an investigation or charges? Usually, it is to send a message.
One recent example was when U.S. Attorney General William Barr announced charges against four Chinese nationals for hacking Equifax.
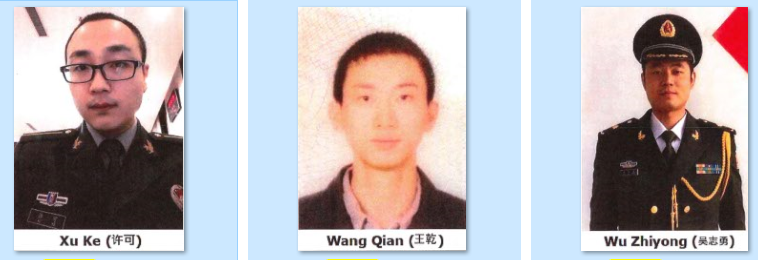
They were part of the People's Liberation Army (PLA) of China's military.
"Today, we hold PLA hackers accountable for their criminal actions, and we remind the Chinese government that we have the capability to remove the Internet's cloak of anonymity and find the hackers that nation repeatedly deploys against us."
And it underscores a U.S. government mind shift during the last few years. We wrote about this in 5 Cyber Changes Homeland Security Is Making—and a Warning to Digital Foes.
And perhaps it alerts the rest of us, as well.
It helps us understand that we are up against a cybercrime ecosystem where our personal information, and our organization's data, can be bought and sold as easily as we might buy something on Etsy or through PayPal.
[Related podcast: The Enterprise Business Model of Cybercrime]




