The COVID-19 pandemic has been an incredibly wild ride for digital meeting platform Zoom.
And now there are renewed questions about the company's commitment to privacy and its willingness to work with law enforcement.
Before we get to that, here is how we arrived at this point in Zoom's wild ride.
Zoom privacy and cybersecurity ups and downs
UP: The world went remote and Zoom usage exploded to record numbers—the kind of growth that XPAN Law Group's Michael Simon called a-historic.
"There are a whole bunch of virtual meeting systems out there and here is Zoom, they have captured 90% of the attention, maybe 99% of the attention."
DOWN: All of the attention led to incredible scrutiny of the platform.
Some users sued over alleged privacy violations.
Zoom admitted the end-to-end encryption it claimed to offer was quite different from the cybersecurity community's definition of the privacy feature.
And then researchers at Toronto's Citizen Lab discovered some North American meeting traffic was being routed through servers in China:
"During a test of a Zoom meeting with two users, one in the United States and one in Canada, we found that the AES-128 key for conference encryption and decryption was sent to one of the participants over TLS from a Zoom server apparently located in Beijing, 52.81.151.250. A scan shows a total of five servers in China and 68 in the United States that apparently run the same Zoom server software as the Beijing server."
Plus, who can forget the Zoom-bombing, where hackers secretly joined meetings and then displayed racist, graphic, or sexual material on the screen? Things seemed to be heading downhill quite fast.
UP: Zoom gave users meeting routing controls, announced a 90-day plan to boost cybersecurity, quickly updated features so meeting hosts could reduce the risk of Zoom-bombing, and re-deployed all engineers to work on privacy and security features.
And Zoom's CEO, Eric Yuan, personally stepped up to explain how his company seemed to go from COVID-19's superstar to operating under a cloud of suspicion.
"...our platform was built primarily for enterprise customers – large institutions with full IT support... thousands of enterprises around the world have done exhaustive security reviews of our user, network, and data center layers and confidently selected Zoom for complete deployment.
However, we did not design the product with the foresight that, in a matter of weeks, every person in the world would suddenly be working, studying, and socializing from home. We now have a much broader set of users who are utilizing our product in a myriad of unexpected ways, presenting us with challenges we did not anticipate when the platform was conceived."
These quick actions earned praise from many CISOs around the world, who got what he was saying and were impressed with what he was doing. And the Zoom team has been regularly updating its security and privacy improvements since that time.
New Zoom controversy over encryption and working with police
UP & DOWN: This week, Zoom announced that its earnings exceeded expectations as business continued to surge. Then it got hit by a tweet read 'round the world from a Bloomberg report:
Zoom's CEO says he won't encrypt free calls so Zoom can work more with law enforcement: "Free users, for sure, we don't want to give that because we also want to work together with FBI, with local law enforcement, in case some people use Zoom for the bad purpose," Yuan said.
The idea that Zoom was happily cooperating with law enforcement and limiting true end-to-end encryption led to a Twitter firestorm, including some publicly announcing they decided to cancel their Zoom subscriptions:

Is Zoom letting law enforcement into meetings?
This raised the question of whether Zoom might allow law enforcement into meetings or share meetings of its free level users with police.
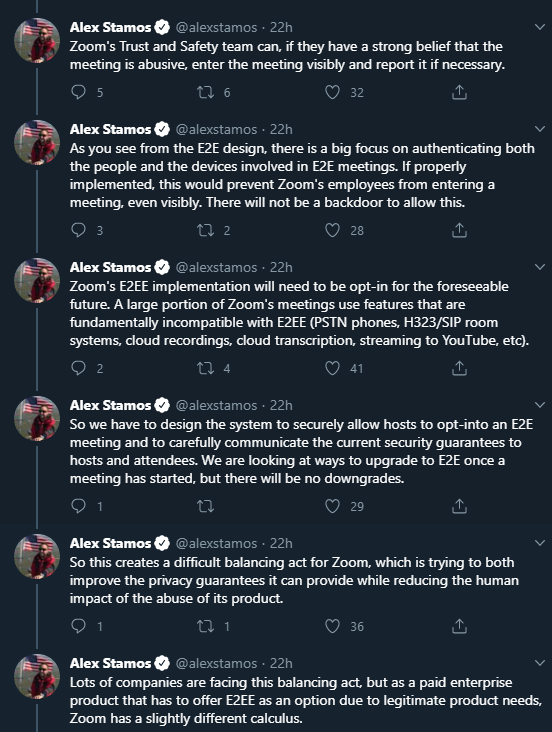
Former Facebook CSO Alex Stamos, who was brought in to help Zoom navigate privacy and security issues, then began a long thread of tweets to do what the company considers setting the record straight.
It's true that Zoom is not giving free users full end-to-end encryption. However, it's also true that Zoom is not letting police peruse its platform. But the company itself can investigate abuse.
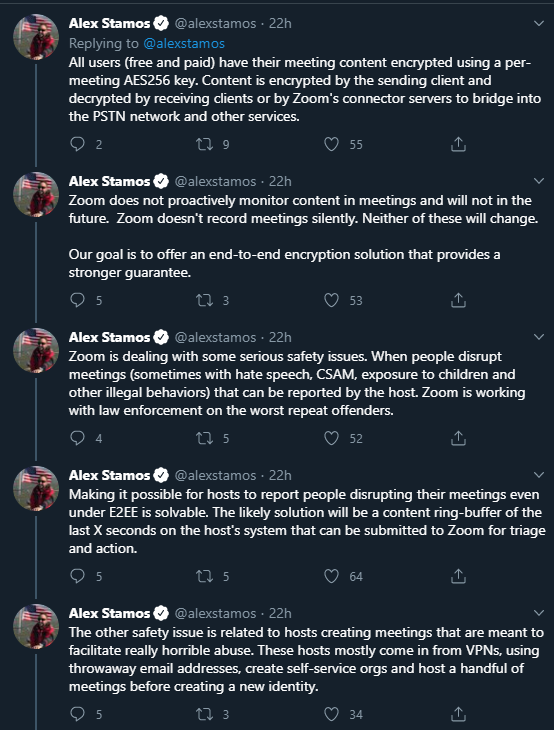
In other words, Zoom admits its platform is being used by criminals, and it is doing something about it.
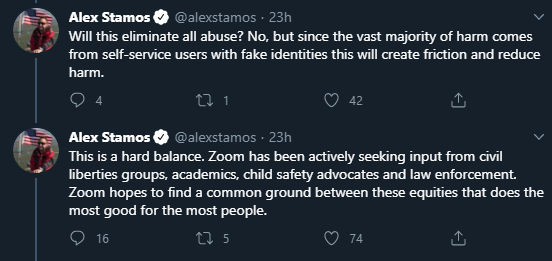
This led to a changed response by some, but certainly not all, on Twitter.
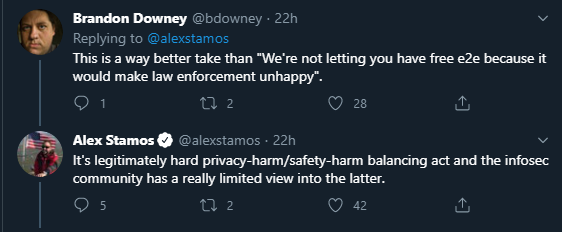
@bdowney wrote:
"This is a way better take than 'We're not letting you have free e2e because it would make law enforcement unhappy.'"
@alexstamos responded to that tweet:
"It is legitimately hard privacy-harm/safety-harm balancing act and the infosec community has a really limited view into the latter."
Clearly, Zoom's wild ride continues.
Have remote work tools like Zoom killed our privacy?
Although this article has focused on Zoom, it is just one remote work tool among many.
Has our dependence on these tools killed privacy as we know it?
We asked cyber attorney Michael Simon, of XPAN Law Group, about this very question. He has a very strong response.
"I see people write that privacy's done, it's over with. I've got friends in the government who tell me, oh, it is all over. No, it's not. This is the opposite.
Now we're going to have to take and build privacy and cybersecurity far more into the things that we do, because now we're all using primarily these mechanisms."
And Simon is optimistic this will happen and is already happening at companies like Zoom.
Listen to his interview on the SecureWorld podcast: Zoom, Remote Tools, Privacy, and Cybersecurity:
Related privacy podcast
If you are interested in privacy and technology, also check out our interview with The Privacy Professor, Rebecca Herold: COVID-19 Contact Tracing: Privacy and Cybersecurity Problems:




