UPDATE on 1/31/20: This case has been resolved. See our follow-up here: Coalfire Pentesters 'Exonerated,' Charges Dismissed
A small blog post sparked significant debate within cybersecurity circles.
The post announced that two pentesters are now wearing orange jumpsuits after police arrested them inside a county courthouse in the middle of the night.
The pair set off an alarm on their way in.

Justin Wynn, of Naples, Florida, and Gary Demercurio, of Seattle, Washington, are charged with third-degree burglary and possession of burglary tools. They were held on $50,000 bond.
[RELATED: Coalfire CEO on Pentester Arrests: 'Heroes Not Criminals']
Original court statement on pentest arrests
This happened in the Dallas County Courthouse in Adel, Iowa. Here is the complete statement from the Iowa Judicial Branch, which paints a picture of the situation:
"State Court Administration (SCA) is aware of the arrests made at the Dallas County Courthouse early in the morning on September 11, 2019. The two men arrested work for a company hired by SCA to test the security of the court’s electronic records.
The company was asked to attempt unauthorized access to court records through various means to learn of any potential vulnerabilities. SCA did not intend, or anticipate, those efforts to include the forced entry into a building.
SCA apologizes to the Dallas County Board of Supervisors and law enforcement and will fully cooperate with the Dallas County Sheriff’s Office and Dallas County Attorney as they pursue this investigation.
Protecting the personal information contained in court documents is of paramount importance to SCA and the penetration test is one of many measures used to ensure electronic court documents are secure."
The pentesters work for Coalfire Cyber Risk Management Advisors and were performing a $75,000 pentest project, according to a contract obtained by SecureWorld.
The company's website couches its technical services overview like this:
"Security today requires you to think—and act—like an attacker. By applying knowledge gained through industry-recognized vulnerability research, tool and exploit development, and technical testing experience, Coalfire Labs simulates an adversarial attack against your product or business."
We did not see physical pentests listed, however, we now know they offer that service.
Unanswered questions about pentester arrests
When this story broke, we focused in on key questions: what was the scope of the pentest project? And did the men go outside the scope of the agreement?
This is a question #cybersecurity people discussed on social media and in our blog comments.
We like what pentester Adrien de Beaupré posted in a pentesting Q&A article about mistakes pentesters can make:
Q: What is the single biggest mistake that a pen tester can make?
A: Violating the rules of engagement or going out of scope. The rules of engagement include the laws and ethical guidelines as well as those types of tests that are allowed to be performed in that engagement. The scope are those things that you are allowed to test in that engagement. Going out of bounds on either of these can not only be career limiting, but also freedom limiting. When in doubt always go back to the written rules of engagement and scope. Ask for clarification or modification if required. There is no cheating in penetration testing. Only those things that are illegal, immoral, unethical, or illogical.
Did this situation cross the line into any of these things? Or was it some sort of misunderstanding that the scope of the pentest included physical penetration testing? Was proper communication all that went wrong?
Updated statement from Iowa courts
SecureWorld News reached out to the Iowa Judicial Branch and Coalfire to ask about the scope of the contract with the pentesters.
The original response from Iowa court officials was this:
"We are not releasing the contract, because it includes sensitive information related to data security that could put the personal information contained in court documents at risk. Judicial branch information or records that deal with personal safety, emergency preparedness, or emergency response are exempt from having to be produced pursuant to Chapter 22 of the Iowa Code."
Now, that has changed and the Courts and Coalfire decided to share redacted documents that indicate the scope of work.
New pentest scope of work documents and PDF
Two of the documents newly obtained by SecureWorld hit the question of pentest scope head on.
Let's look at the key part of the Coalfire and Iowa Judicial Branch rules of engagement agreement:
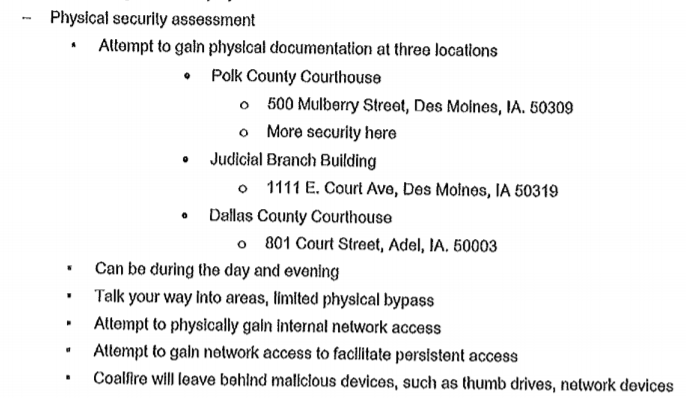
As you can see, it specifically includes a "physical security assessment," at several locations, which "can be during the day and evening, talk your way into areas, limited physical bypass...."
Does this allow breaking and entering and setting off an alarm at the courthouse?
When police found the men in the courthouse, as the alarm was going off, the men claimed they were working on physical security: "... to test out the courthouse alarm system's viability and to gauge law enforcement's response time." That is according to the Des Moines Register.
To answer this question of whether "breaking in" was within the scope of the pentest, let's look at a key part of the Coalfire Labs Social Engineering Authorization document:
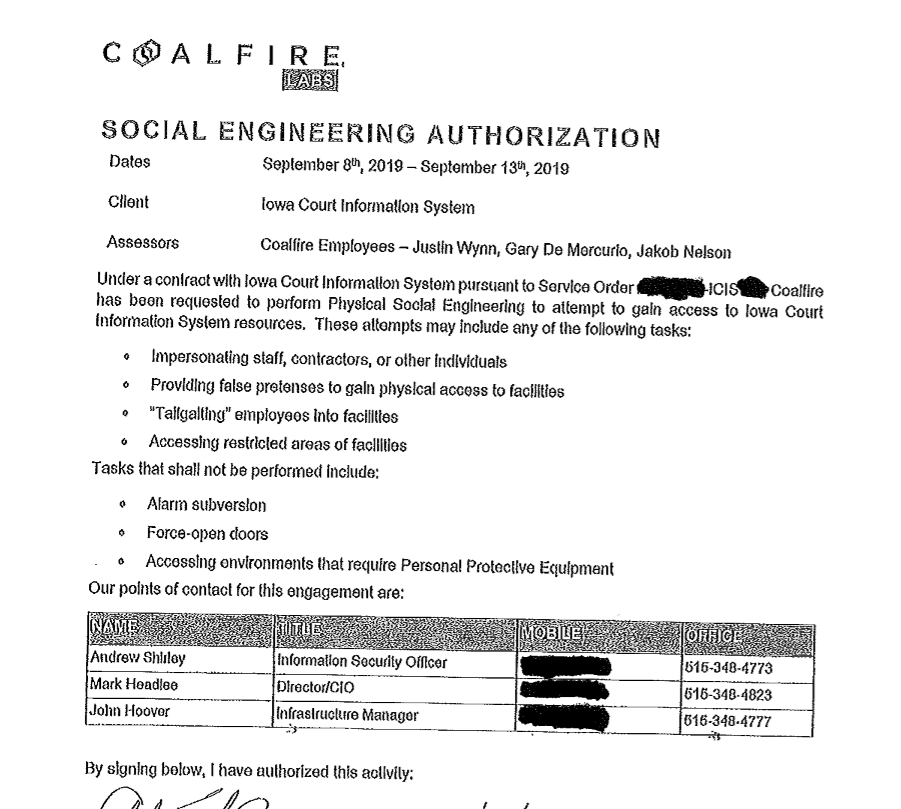
Can you read a couple of the final bullet points in this document? It states:
Tasks that shall not be performed include:
• Alarm subversion
• Force-open doors
Did they force open doors? Maybe they came in through a window instead. Would that be within scope?
That's a great question.
What is happening now in the pentester arrest case?
We know this much: There are two investigations, happening at the same time, according a the latest post by the Iowa Judicial Branch:
"Coalfire and State Court Administration believed they were in agreement regarding the physical security assessments for the locations included in the scope of work.
Yet, recent events have shown that Coalfire and State Court Administration had different interpretations of the scope of the agreement. Together, Coalfire and State Court Administration continue to navigate through this process. To that end, the Iowa Judicial Branch and Coalfire will each be conducting independent reviews and releasing the contractual documents executed between both parties."
Based on what these documents reveal and your experience in cybersecurity, what are your thoughts on this case? Could this have been a simple misunderstanding?
Please let us know in the comments below.
And in the meantime, read these complete documents for yourself:
Coalfire / Iowa Judicial Branch Social Engineering Agreement
Coalfire / Iowa Judicial Branch Scope of Agreement
PenTester Arrest Update: Read Our Follow Up, 'Heroes Not Criminals'




