Students, teachers, and parents across the country have been forced to adapt to remote learning, which can be challenging for a lot of different reasons.
Students and teachers can have their connection interrupted during class, communicating essential topics and ideas is much harder, group projects are a mess. The list of things that can go wrong with remote learning goes on and on.
Now, an unusually large number of students and teachers must add another difficulty to the list: a ransomware attack.
K-12 schools ransomware attacks at record pace
The FBI, CISA, and the Multi-State Information Sharing and Analysis Center (MS-ISAC) recently revealed that the number of ransomware incidents against K-12 districts increased dramatically at the beginning of fall 2020 classes.
And the MS-ISAC says K-12 school districts are now the most likely to suffer from and report a successful ransomware attack.
K-12 districts now top ransomware target
From January through July, 28% of ransomware incidents involved K-12 schools.
However, when schools began to start up again in August and September, that number rose to 57%, making K-12 districts the most likely entities in the United States to suffer from and report a ransomware attack.
The FBI, CISA, and MS-ISAC also revealed that many of these attacks are extortion based:
"In these attacks, malicious cyber actors target school computer systems, slowing access, and—in some instances—rendering the systems inaccessible for basic functions, including distance learning. Adopting tactics previously leveraged against business and industry, ransomware actors have also stolen—and threatened to leak—confidential student data to the public unless institutions pay a ransom."
Now, let's look at some specifics.
Specific ransomware and malware strains affecting schools
The MS-ISAC also identified the five most common ransomware strains used to attack schools from January through September. These five strains are Ryuk, Maze, Nefilim, AKO, and Sodinokibi/REvil.
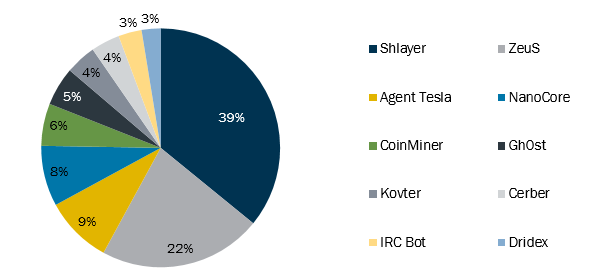
Aside from ransomware, malware has also been a problem for K-12 schools. CISA has put together a chart which represents the ten most common malware strains that have affected state, local, tribal, and territorial (SLTT) educational institutions this year, Shlayer and ZeuS being the top two.
Though not as prevalent as ransomware and malware, there have been reports of DDoS attacks on schools, as well as video conference interruptions by cyber actors.
Mitigations against cyberattacks
The FBI and CISA are encouraging schools to maintain business continuity plans to minimize interruptions due to a cyberattack. Without proper planning and preparation, schools may be unable to continue classes and administrative operations.
Here are some recommendations for best network practices:
- Patch operating systems, software, and firmware as soon as manufacturers release updates.
- Check configurations for every operating system version for educational institution-owned assets to prevent issues from arising that local users are unable to fix due to having local administration disabled.
- Regularly change passwords to network systems and accounts and avoid reusing passwords for different accounts.
- Use multi-factor authentication where possible.
- Disable unused remote access/RDP ports and monitor remote access/RDP logs.
- Implement application and remote access allow listing to only allow systems to execute programs known and permitted by the established security policy.
- Audit user accounts with administrative privileges and configure access controls with least privilege in mind.
- Audit logs to ensure new accounts are legitimate.
- Scan for open or listening ports and mediate those that are not needed.
- Identify critical assets such as student database servers and distance learning infrastructure; create backups of these systems and house the backups offline from the network.
- Implement network segmentation. Sensitive data should not reside on the same server and network segment as the email environment.
- Set antivirus and anti-malware solutions to automatically update; conduct regular scans.
The FBI and CISA suggest that by establishing security policies and plans, schools will be able to successfully address current threats posed by cyber actors.
And hopefully, that will reduce the chances of a ransomware attack making online learning even more difficult for your local schools.





