Shawn Tuma thought Y2K would be his rocketship to notoriety. Instead, Y2K was simply hype, followed by a flop.
Now, it's nearly 20 years later, and the tech-focused Tuma is internationally known for something else: cybersecurity and data privacy law. He is spending more time than ever on IoT as companies try to secure the massive amounts of data these devices collect.
"Cybersecurity and the Internet of Things are not Y2K; we will not see this just go away. This is both a real and a serious issue," he told hundreds of information security leaders on this week's SecureWorld web conference, "Securing IoT Data: Compliance, Privacy & New Regulations." Tuma is a partner at Scheef & Stone, LLP.
"How are you supposed to protect data that you don't know exists, and how are you supposed to protect your company against the risks of data that you don't know exists? In today's world with IoT devices, it's now an exponentially larger problem than it was just a couple of years ago."
Devices within your corporate headquarters, the ones you have deployed around the world, even personal devices your employees bring through the door. Each one is collecting and often transmitting data.
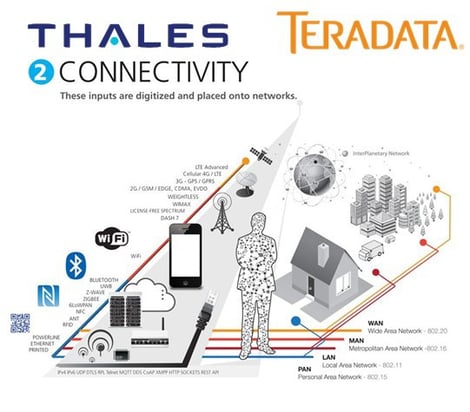
"Right now companies are managing devices in the billions, and we'll be managing devices in the trillions in very short order. And think about the numbers we'll be managing 'data elements' in. This is just huge," said Andrew Lance of Thales e-Security, who delved into some critical details on IoT data and also painted a big picture of the IoT itself, as you can see from his slide.
This was a fantastic and interactive web conference with a large number of questions from your peers. Topics covered include: GDPR and IoT Data, new laws around data security in the U.S., and how government agencies are cracking down on companies relating to data. The group also discussed strategies for compliance and securing the data.
~
Watch the web conference on demand here.
Join your peers on the next SecureWorld web conference:
"Risky Business: When End-Users Continue Bad Security Behavior"




