In the continued industry fallout related to the SolarWinds breach, we are about to reach another milestone.
The attack left key SolarWinds' customers compromised, including Fortune 500 companies and U.S. government agencies.
In January 2021, SolarWinds President and CEO Sudhakar Ramakrishna announced in a blog post that the company will be taking "key steps to ensure the security and integrity of the software" they deliver to customers.
One of these steps includes revoking the code-signing certificate used by SolarWinds to sign the affected software versions, which will happen on March 8, 2021.
SolarWinds new digital code-signing certificate
While revoking the affected code-signing certificate is one step in the recovery process, the next will be getting the new code.
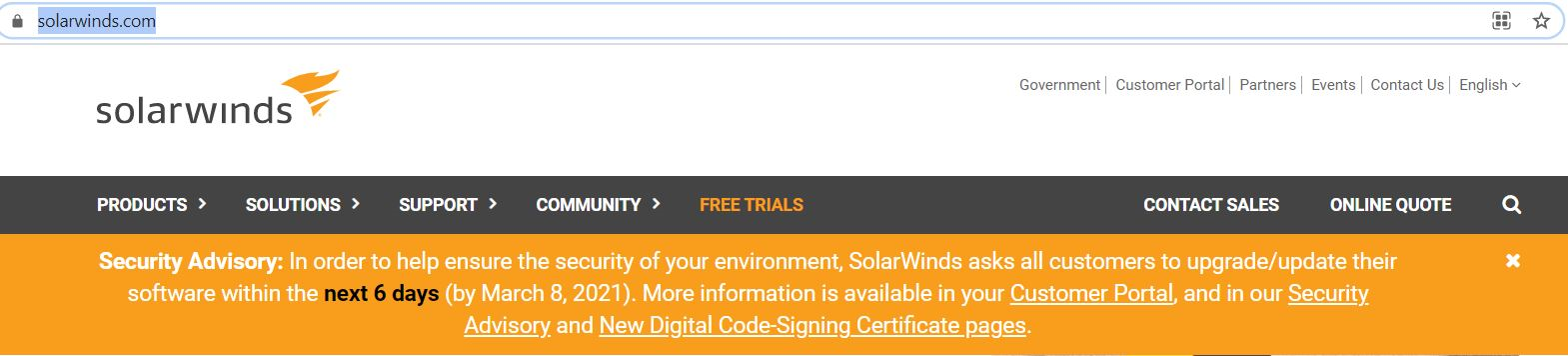
And this move is time sensitive if you are a SolarWinds customer. The company's website is displaying a countdown:
Thousands of organizations will need to update their software within the next few days. Here's why this is so crucial, even if you don't use its impacted service:
"Regretfully, the same digital code-signing certificate used to sign our Orion Platform software affected by the SUNBURST vulnerability was also used to sign additional SolarWinds products not known to be affected by SUNBURST. While this does not mean all products are compromised, it does mean the day-to-day operation of any software signed by the compromised digital code-signing certificate may be impacted by a user's operating system, antivirus, or endpoint protection software when the certificate is publicly revoked on March 8, 2021.
We've obtained new digital code-signing certificates and have rebuilt the affected versions, have re-signed our code and have re-released all of the products previously signed with the certificate to be revoked. To ensure the performance of your SolarWinds product(s), you must upgrade to these new builds before March 8, 2021."
For more information regarding SolarWinds' code-signing certificates, you can read the most recent blog post.





