The original story sent shock waves through the tech world: China is implanting small microchips on motherboards to spy on customers like Amazon and Apple.
Supermicro's motherboards, made in China, were named in the story of an alleged supply chain security attack. Had one of the company's third-party vendors gone rogue on behalf of the Chinese government?
Questions started to arise about the claims, and denials from Apple and Amazon pushed back against the story. Still, doubts lingered, because China likes to win and often uses cyberspace to carry out key initiatives.
Supermicro motherboard audit
Now, however, Supermicro is reporting back on two months of supply chain security testing of its motherboards, done with the assistance of an unnamed third-party investigations firm:
"A representative sample of our motherboards was tested, including the specific type of motherboard depicted in the article and motherboards purchased by companies reference in the article, as well as more recently manufactured motherboards."
Supermicro supply chain security audit results
The company says the audit results found no hidden microchips or hardware on any of the motherboards and that the company is vindicated:
"... no government agency has ever informed us that it has found malicious hardware on our products; no customer has ever informed us that it found malicious hardware on our products
The company went so far as to create a new video, where Supermicro shows how it maintains supply chain security. Watch the video for more:
Supermicro also makes this point: Any malicious hardware added to any layer of its motherboards would cause them to malfunction and be rejected.
Which is another reason Supermicro rejects Bloomberg's original
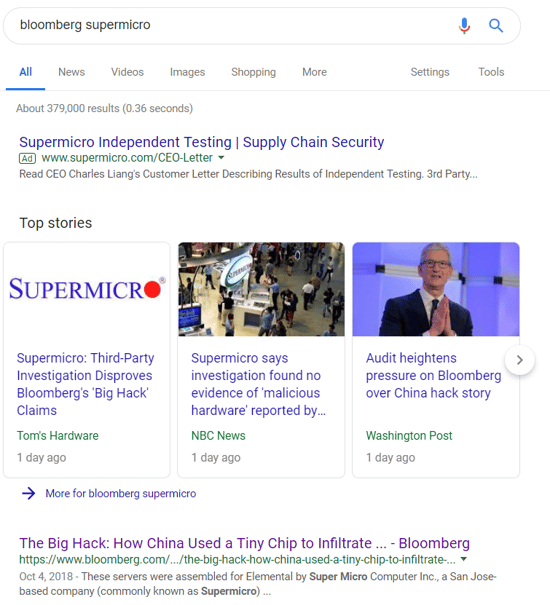
Try this Supermicro Google search
Supermicro is sharing its audit results with the world, and that includes buying a Google ad on a crucial page. If you search "Bloomberg Supermicro," the top result is no longer the Bloomberg article, it is Supermicro's letter denying the claims and giving audit results: