The name? VandaTheGod.
The track record? A seven-year hacktivist campaign of defacing nearly 5,000 websites
The identity? Until recently, unknown.
Who is VandaTheGod?
When the list of entities you've hacked includes the governments of multiple countries, it's safe to say you have a reputation.
And for seven years, hacktivist VandaTheGod added to that notoriety. Check Point Research detailed the hacker's numerous campaigns:
"The hacker targeted governments in numerous countries, including: Brazil, the Dominican Republic, Trinidad and Tobago, Argentina, Thailand, Vietnam, and New Zealand. Many of the messages left on the defaced websites implied that the attacks were motivated by anti-government sentiment, and were carried out to combat social injustices that the hacker believed were a direct result of government corruption.
VandaTheGod didn't just go after government websites, but also launched attacks against public figures, universities, and even hospitals. In one case, the attacker claimed to have access to the medical records of 1 million patients from New Zealand, which were offered for sale for $200."
And VandaTheGod certainly seemed to enjoy the attention. The alias was active on Twitter, often mocking attack victims and even linking tweets like the one below on the pages of hacked websites:
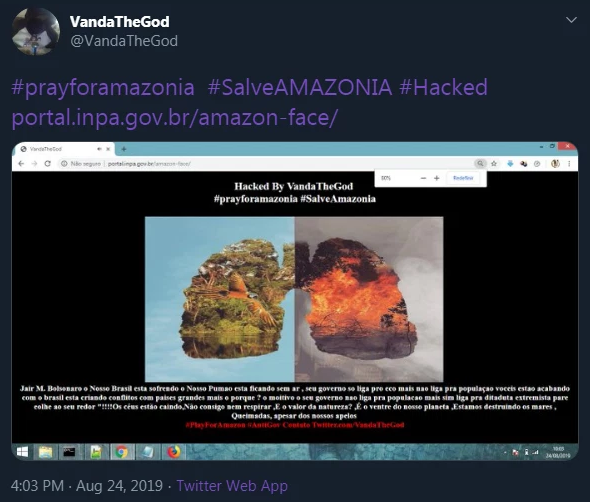
The hacker also used Twitter to promote the media attention his hacks received and update other users on his ultimate goal of hacking 5,000 websites:

Social media was a prominent outlet for VandaTheGod to boast about his hacks and connect with other hackers. It's also what made his true identity available to investigators to find.
Bringing a hacktivist to justice
According to Check Point Research, VandaTheGod's long history on social media left plenty of breadcrumbs for researchers to follow.
"VandaTheGod's major role in several hacking groups, as well as their love of publicity, meant that they stayed in touch with others in the hacking community through numerous social media accounts, backup accounts in case of takedown, email addresses, websites and more."
In one example, an email address VandaTheGod provided linked to a user in Brazil.
In other tweets, the hacker also included screenshots of his hacks. But the screens also tended to include revealing personal information, like potential Facebook accounts.
By cross-referencing Facebook users to websites registered with the email VandaTheGod provided, and comparing the backgrounds of photos for similarities, Check Point Research managed to pinpoint the hacker's personal Facebook account.
"Check Point reported these findings to the relevant law enforcement. All of the detailed social media profiles still exist, but many of the photos in the attacker's personal profile that overlap with those shared by the VandaTheGod alias were later deleted. Moreover, the activity on these profiles came to a halt toward the end of 2019, and the person has not posted any updates since."
The hacker's location was tracked to Brazil and reported to authorities there. No word yet on whether he has been apprehended.





