In June, Wombat Security released its 2017 User Risk Report, which featured the results of a survey of more than 2,000 working adults—1,000 in the US and 1,000 in the UK—who were asked about cybersecurity topics and personal habits related to data and network security. What was revealed in the report was at times heartening, but more often perplexing or even downright frightening.
Low awareness of phishing and ransomware
No survey related to cybersecurity awareness would be complete without queries related to phishing and ransomware. Wombat’s report doesn’t disappoint; its survey repeated two questions the organization originally asked of respondents for its 2017 State of the Phish™ Report: “What is phishing?” and “What is ransomware?”
Wombat did not see a big change in results over the several months that passed between the two surveys. Though it’s somewhat positive to note that 70% of US and UK respondents were able to identify phishing in basic terms, 30% were not able to answer correctly (and 13% of those respondents were not even willing to take a guess).
The figures tied to ransomware recognition were, unfortunately, more dismal. (It’s interesting to note that Wombat’s survey concluded less than 24 hours prior to the spread of the first reports about the global WannaCry ransomware attack.) Fewer than half of respondents (37% in the US and 42% in the UK) were able to accurately identify ransomware’s definition—and 39% of UK respondents wouldn’t even hazard a guess on this multiple-choice query.
The problem gets a bit more concerning when these results are equated to people rather than percentages. Looking at these numbers in the context of a 2,000-person organization:
- 3 out of every 10—or 600 people—would not know what phishing is
- 6 out of every 10—or 1,200 people—would not know what ransomware is
If you are operating under the assumption that your employees are aware of what phishing and ransomware are, it’s probably time to reevaluate. As well, it’s important to note that awareness is not the same as actionable knowledge. Even those who are able to correctly point out the definitions of these terms may not have the skills needed to recognize and avoid these attacks in real-world settings.
Improper use of corporate devices
In today’s technology-driven workforce, organizations must place a lot of trust in their employees to “do the right thing” with the devices, data, and systems they are given access to. Wombat’s User Risk Report also took a look at whether employees are following best practices or whether organizations’ trust is misplaced.
On this topic, the report revealed a significant difference between the two survey groups; 71% of US respondents indicated they regularly use corporate-issued devices (PCs, smartphones, and/or tablets) at home vs. 39% of UK respondents. (It’s worth noting that Wombat first caught a glimpse of this work life/personal life separation with UK employees in the aforementioned 2017 State of the Phish survey.)
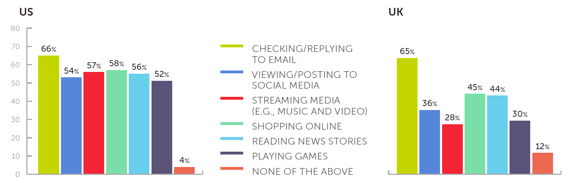
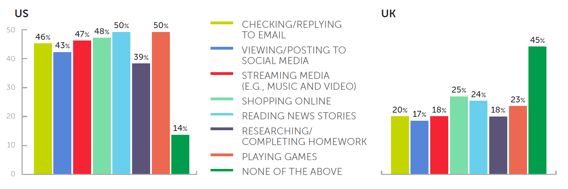
But what Wombat dug further into is of particular interest: namely, the personal activities these employees use their corporate devices for and the activities they allow their friends and family to complete on these same devices. As you’ll see from the charts below, organizations are not as secure as they might think they are:
Question: What personal activities do you perform on your corporate devices?
Question: What activities do you allow trusted friends and family members to perform on your corporate devices?
As Wombat noted in its User Risk Report, there is clearly much to be done on the security awareness and training front when it comes to managing end-user risk. To see more about the types of behaviors and misconceptions revealed in the international survey—including those related to use of social media, open-access WiFi, and VPNs—download your copy of the report on the Wombat Security website.





