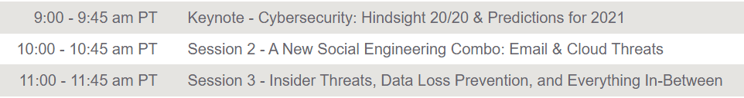
Join Proofpoint and SecureWorld as we bring you a free online summit to review the biggest 2020 cybersecurity trends, examine the lessons learned, and explore top threat predictions for 2021. Our top industry experts will discuss real-world examples and best practices for protecting your company's most important assets: your people and your data!
All sessions will be eligible for CPE credits with ISC(2).
2020 has brought many cybersecurity challenges many did not foresee. From protecting against worldwide pandemic-related threats to accommodating mass remote workforces overnight, many companies struggled with the new security risks while still maintaining business continuity. While hindsight is 20/20, businesses need to reexamine their cybersecurity strategies to better prepare for the coming new year.
Join our experts as they review real-world scenarios of cyber attacks from this year, deep dive into the top threats for next year, and explore how you can better protect your most valuable assets: your people and your data. In this session, we'll cover:
• The most significant cyber trends and lessons learned in 2020
• Top predictions for the threat landscape going into 2021
• A people-centric approach to help support your security efforts
Cybercriminals are increasingly blending both email and cloud vectors, whereby a single malicious email can lead to an infiltrated cloud account. Since 94% of data breaches start with attacks targeting people via email, organizations need a holistic approach and solution to combine security efforts across all channels. So how is this achieved? Proofpoint's threat research team found that Microsoft O365 has become attackers' playground. Legitimate filesharing abuse and OAuth token abuse by malicious 3rd party apps have become more common. Attackers are leveraging cloud platforms to host malicious applications and spread malicious files via email, resulting in email account compromise (EAC).
Join our experts as they expose how attackers use cloud services, like Microsoft SharePoint, to redirect people to phishing sites, phish for login credentials and Office 365 OAuth tokens, or compromise a cloud account to launch a BEC/EAC attack. In this session we’ll cover:
• Trends and modern threat landscape
• Case studies on how threat actors leverage legitimate cloud services to launch attacks
• How to address these sophisticated hybrid attacks
Traditional DLP hasn't lived up to its promises. That's because data loss begins with people—whether they are negligent, compromised by external actors, or malicious insiders. Today, data loss prevention (DLP) and insider risk are top of mind for companies with a distributed workforce and increasing reliance on technology. So how can you better protect your organization?
Join our experts for a conversation on why organizations need to take a modern, people-centric approach that provides visibility and context into content, user behavior, and threat insights to mitigate this risk. In this webinar, you'll learn:
• The importance understanding user risk profiles
• How to better understand and respond to people-led data breaches
• Real-world examples and best practices to improve your data and user security
Join for all the sessions or just the ones you have time for. Don't worry, we'll record them all for you should you prefer to check these sessions out on-demand.
For additional details, visit: https://go.proofpoint.com/cybersecurity-esummit-hindsight-predictions.html
Generously supported by:

With almost 20 years of professional experience in the information security industry, Ryan has provided cybersecurity counsel to global government delegations including Jordan, North Macedonia, Peru, and Spain. He also works with the National Governors Association and is a board member of the National Cyber Security Alliance and the Cybersecurity Technical Advisory Board.

Mark Eggleston is a senior executive specializing in security and privacy programs. His unique background and expertise in IT program and people management, combined with his diverse experience in healthcare, has positioned him as a thought leader and frequent speaker.
Mark currently serves as Vice President, Chief Information Security Officer and Privacy Officer, at Health Partners Plans, a Philadelphia-based health insurance company. He leads the maturation of various security technologies and privacy initiatives and manages a business continuity and disaster recovery program.
He started his professional career serving as a Program Manager and Psychotherapist at a hospital serving children and adolescents. Later, he helped develop a HIPAA privacy and security compliance program for a geographically dispersed health care provider organization and later, a local health plan.
Mark has an undergrad degree in Psychology, a Masters in Social Work, and a Post Baccalaureate Certificate in MIS, and maintains GSEC, CHPS, and CISSP certifications. He is also a founding chair adviser for the CyberEdBoard Global Community.


Roie is a versatile and seasoned security research and software development manager with over 15 years of professional experience. He's currently the security research director at Proofpoint, leading a team that's focusing on cloud threats, detection and research.

Brian has over 20 years of professional IT Security experience. He has worked in a variety of Product Development, Product Management, Systems Engineering, Business Development and Sales roles. Prior to joining Proofpoint, Brian served as the senior analyst director at Gartner.

Randy Raw is VP of Information Security, serving as the Information Security Officer at Veterans United Home Loans in Columbia, Missouri. He has more than 25 years of experience in both public entities and private industry, having built several Information Security programs from the ground up. He is a proponent of risk-based, layered security measures that utilize both preventative and detective approaches to achieve the right solution for the organization. Randy is a CISSP and is active in the Central Missouri InfoSec community. He has spoken at SecureWorld on many technical topics and turns his focus towards helping others move from the technical trenches to a leadership role.
Questions? Have an idea for a topic? Interested in sponsoring our web programs?